What An IT Risk Assessment Can Save You
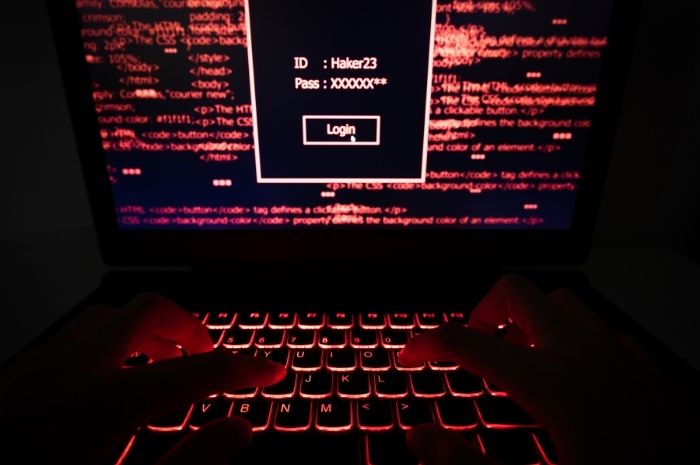
Thanks to the horrible stories you see on the news about cyberattacks, customers are worried about IT risks like ransomware, foreign nation-state hackers, cryptocurrency scams, and phishing. Unfortunately, they are blissfully unaware of the major risks that they are taking every day. These risks include the lack of reliable backups, misconfigured security when it comes…